Tags
partition magic,, resize partition, shrink partition, shrink partition on Windows Server 2008, shrink volume, Windows partition magic
Perhaps disk management tool occurs to many users when they are about to shrink partition on Windows Server 2008. Compared with Windows Server 2003, Windows Server 2008 is equipped with two functions to resize partition: “Shrink Volume” and “Extend Volume”. Users can select a partition, then right click mouse and then click “Shrink Volume” function to shrink partition. However, this function only operates on the tail end of a partition, which is limited.
Besides the built-in disk management tool, users can also use professional Windows partition magic server to shrink partition on Windows Server 2008. It can be downloaded from http://www.partitionwizard.com/partition-manager-server.html.
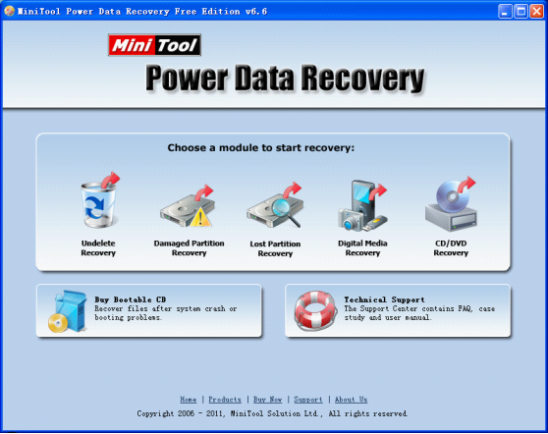
How to shrink partition with the Windows partition magic?
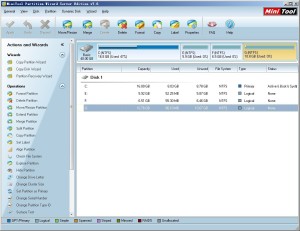
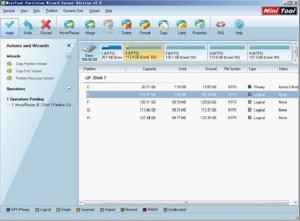
Launching the professional partition magic, users will see the following interface.
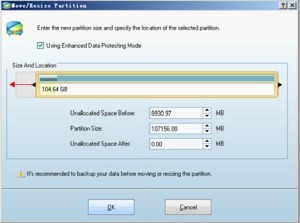
We are going to shrink Partition G:. Select it and click “Move/Resize Partition” function. The following interface will be shown. 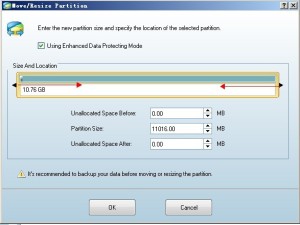
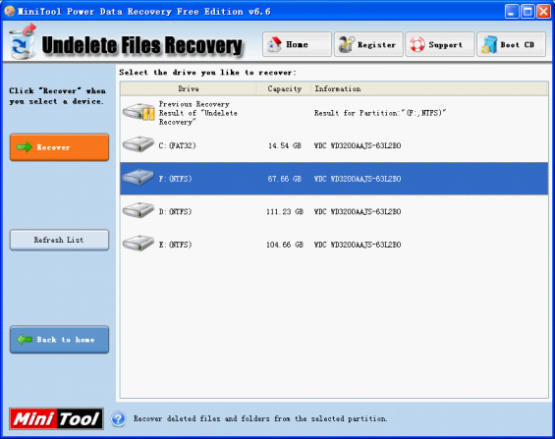
Please drag the two arrows towards the middle to shrink partition. Or we can also input exact values in the textboxes below to shrink partition. Then click “OK” to go back to the main interface.
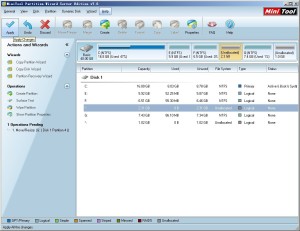
We can see two unallocated spaces (marked with *) appear respectively in front of and behind Partition G:. Please click “Apply” to execute the operation.
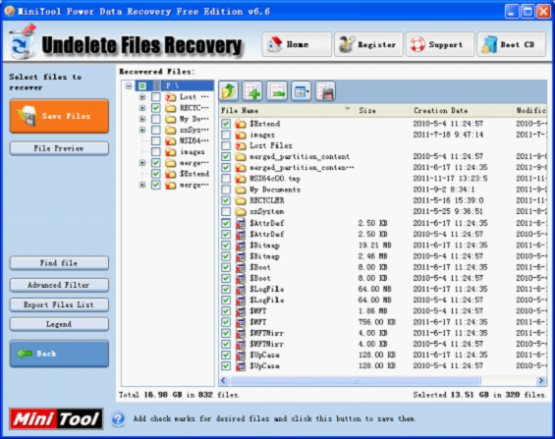
Seen from the above demonstration, this Windows Server partition magic is able to function on both ends of a partition. And the unallocated spaces can be used to extend other partitions or create new partitions.
Users can also see “Split Partition“ from the main interface. This function is different from shrinking partition. It can split a large partition into two smaller ones. We will show it to help users distinguish them. Take Partition G: for example.
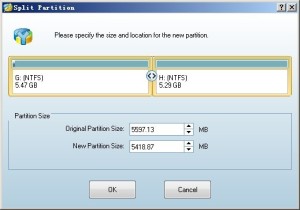
Select Partition G: and click “Split Partition” function. Users will see the following interface.
Please drag the middle button to resize partitions (or we can also set partition size in the textboxes below). Then click “OK” to go back to the main interface. 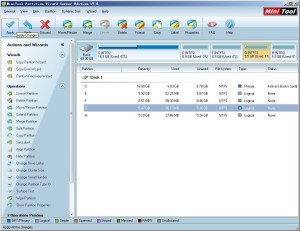
Partition G: becomes smaller and a new partition appears behind it.
Through the above comparison, users may have known the differences between shrinking partition and splitting partition. There are also another two functions to resize partition: “Extend Partition” and “Merge Partition”. For more information about them, please visit the official website of this Windows partition magic.